| Property | Value |
|---|---|
| Grant type | client_credentials |
| Client auth | private_key_jwt |
| Signing algorithm | RS256 |
| Scope | full_access |
| Token URL | https://api.sixtyfour.ai/oauth/token |
| Discovery URL | https://api.sixtyfour.ai/.well-known/oauth-authorization-server |
Step 1: Go to OAuth Clients
Go to Settings → OAuth Clients.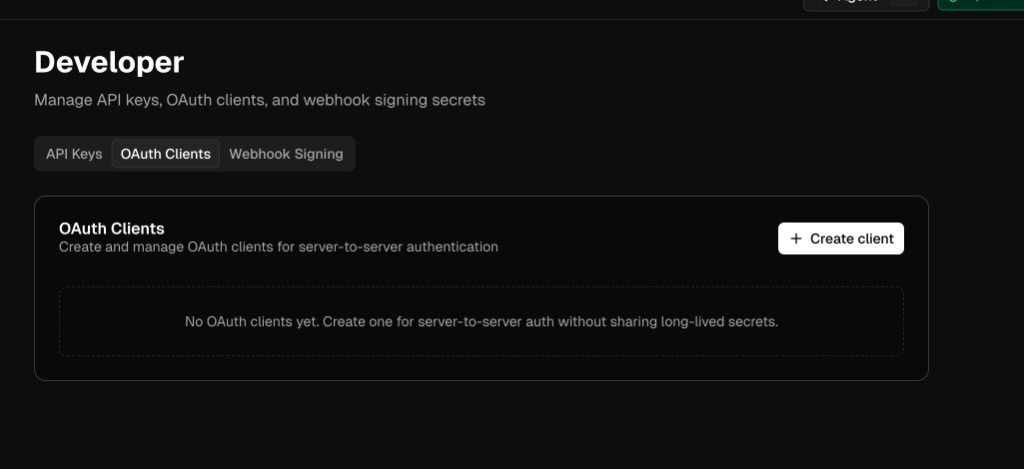
Step 2: Create a client
- Click Create client
- Enter a Client Name (for example,
my-production-app) - Optionally enter a JWKS URL — a public HTTPS endpoint that serves your JSON Web Key Set
The JWKS choice is permanent. Provide a JWKS URL for automatic key discovery and rotation, or leave it blank to upload public keys manually. You cannot switch modes after creation.
- Click Create and continue
client_id and drops you into the client detail view.
Step 3: Configure your key
Pick the flow that matches how you created the client.Option A — JWKS URL
If you configured a JWKS URL, Sixtyfour fetches your public keys from that endpoint automatically. Validate it at any time:- On the client detail page, click Validate JWKS
- Confirm the health indicator shows a green check and a recent validation timestamp
Option B — Upload a public key
If you did not set a JWKS URL, generate an RSA key pair and upload the public half:- Click Upload key
- Paste the contents of
public.pem(including the-----BEGIN PUBLIC KEY-----and-----END PUBLIC KEY-----lines) - Click Upload key
kid) — you’ll include it in the JWT header.
Step 4: Request an access token
Your server signs a short-lived JWT assertion with the private key, then POSTs it to the token endpoint.Step 5: Call the API
Send the token in theAuthorization header on any Sixtyfour API request:
x-api-key. Do not send both headers on the same request. Run the token exchange server-side only — never from a browser.
Managing a client
The client detail page exposes everything you need after setup.Adjust token TTL
Change Token TTL to control how long issued access tokens stay valid. Options are 1 minute, 5 minutes, 1 hour, or 24 hours. Shorter TTLs reduce blast radius if a token is leaked.Rotate keys
If you configured a JWKS URL, publish the new key in your JWKS document and click Validate JWKS. Sixtyfour picks up the newkid automatically on the next fetch.
If you uploaded a public key directly, upload the new key, switch your signer to the new kid, then revoke the old key from the Public Keys table.